

13th August 2020
As organisations are increasingly connecting industrial control networks to the IT environment, cloud applications, and remote workers, the air gap created by the demilitarised zone (DMZ) erodes, and new ways to secure operational technology (OT) networks must be deployed. A... Read More...
12th August 2020
A hacker has published a list of plain text usernames and passwords, along with IP addresses for more than 900 Pulse Secure VPN enterprise servers. ZDNet, which obtained a copy of this list with the help of threat intelligence firm... Read More...
28th July 2020
The U.S. National Security Agency and the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency have issued a joint alert urging critical infrastructure operators to take immediate measures to reduce the exposure of operational technology (OT) systems to cyberattacks.... Read More...
16th July 2020
'Home and remote working' exercise has been added to the Exercise in a Box toolkit. The National Cyber Security Centre launches exercise to help small businesses test their cyber resilience while staff work remotely‘Home and Remote Working’ exercise will form... Read More...
15th July 2020
The COVID-19 pandemic has created disruption and massive change at a scale and rate that many never thought was possible. But with change, even under heart-breaking conditions, can live opportunity. As we invest in reigniting growth, this is an opportunity... Read More...
13th July 2020
While earlier generations of cellular technology (such as 4G LTE) focused on ensuring connectivity, 5G takes connectivity to the next level by delivering connected experiences from the cloud to clients. 5G networks are visualised and software-driven, and they exploit cloud... Read More...
6th July 2020
As the adoption of cloud communications solutions continues to grow, organisations have recognised that all products are not developed, managed, or secured in the same ways. They are rightly asking tough questions about the security, privacy, transparency and reliability of... Read More...
2nd July 2020
After the dust had settled from the move from office to remote work, Cisco took a look at ways you could improve your security posture. In it, they discussed how you can shore up older and personal devices now being... Read More...
1st July 2020
Cyber-security experts have revealed today 19 vulnerabilities in a small library designed in the 90's that has been widely used and integrated into countless of enterprise and consumer-grade products over the last 20+ years. The number of impacted products is... Read More...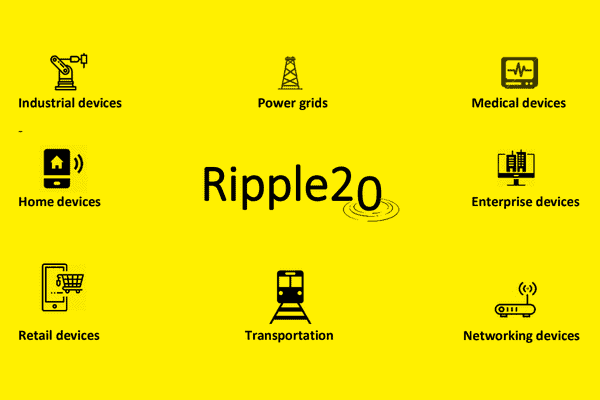
29th June 2020
Announcing the Future of Work 75% of more than 25,000 respondents to a recent IBM survey indicated they would like to work remotely at least occasionally post-COVID. And 54% said they’d like this to be their primary way of working.... Read More...
Copyright 2026. All Rights Reserved